Last week, I attended the Researcher Appreciation Ceremony held alongside the prize ceremony of Jaga the STACK Finale 2022. The Researcher Appreciation Ceremony was held as part of GovTech’s Crowdsourced Vulnerability Discovery Programme (CVDP), where they will present various awards, such as the Top GBBP Researcher award.
I could vividly recall that the entire event was filled with not only students, but also working professionals looking for young and bright individuals for internships or job offers, as the student competition includes categories for a variety of education level (e.g. University). Not forgetting that the organiser also invited the local white hat community to attend this event.
Receiving the Top GBBP Researcher and Most Staunch Supporter Awards
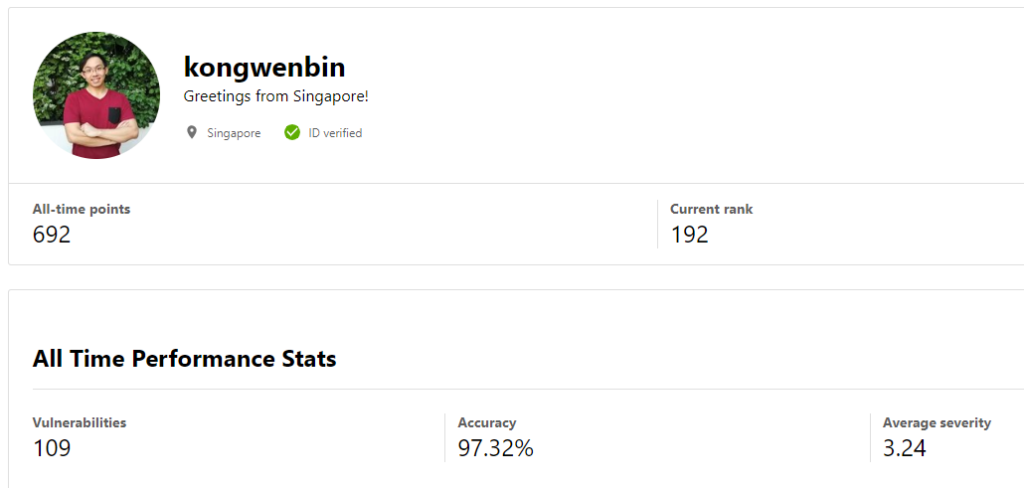
It was an honour to be the recipient of the following two awards:
- Top GBBP Researcher
- Most Staunch Supporter
It was an even greater honour to be able to receive the awards from our Senior Minister of State, Dr Janil Puthucheary.

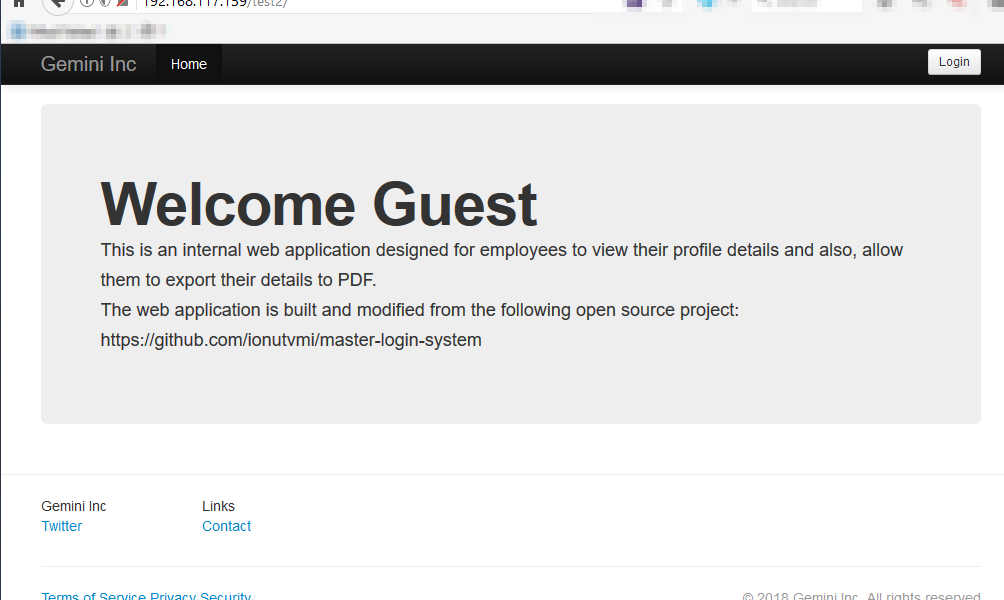
Government Bug Bounty Program (GBBP)
The Government Bug Bounty Program (GBBP) is held multiple times within a year, whereby GovTech, the organiser, will liaise with various Singapore government agencies to invite them onto the program. After they have been on-boarded, they will provide a list of assets allowed to be tested by the invited white hat security researchers.