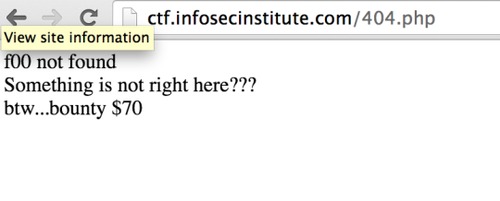
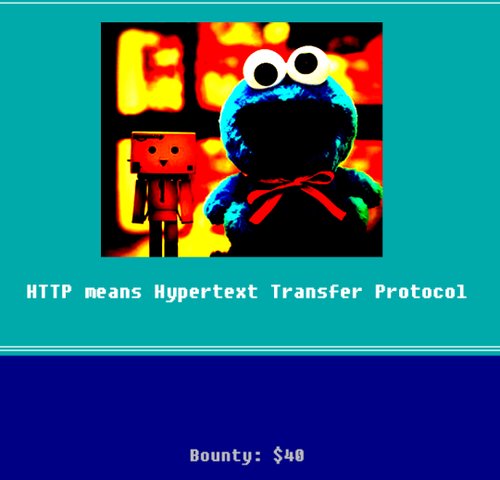
In level 7, we get a page with error 404 – page not found, with the following text,
Take a look at the page source and its cookies, etc., clearly shows that nothing is fishy here. However, did you noticed that the navigation bar at the top of the page is missing?
You are right, return to previous pages and see, e.g. “/levelsix.php” or “/levelfive.php”; they are all using the same format of URL naming. But this page is named as “/404.php”, which breaks the “trend”.
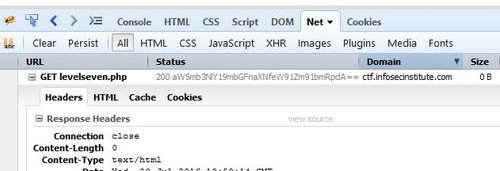
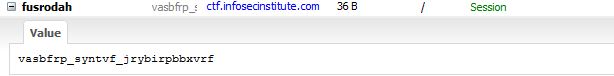
Let’s try to navigate to “/levelseven.php” and see if there is anything… and there you go! A blank page with the flag depicted clearly on the website status. Can you spot it?
Once again, we can see that the flag is base64 encoded in “aW5mb3NlY19mbGFnaXNfeW91Zm91bmRpdA==”, we can decode it using an online base64 decode tool – “infosec_flagis_youfoundit” is the flag.
Back to write-up list for InfoSec Institute CTF #1: Hacking for n00bz